Bluetooth Technology, Bluetooth Working, & Uses of Bluetooth
Last Updated on September 12, 2021 by Engr. Shahzada Fahad
Table of Contents
Bluetooth:
Bluetooth is a wireless technology that is mainly designed to enable wireless communications and used for exchange data over short distances. Bluetooth is local area network. Some key benefits of Bluetooth technology are cable replacement is a file-sharing Internet connectivity and low cost technology. Now whenever Bluetooth devices come within range of one another an electronic conversation determines whether they have data to share or whether one needs to control the other. There is no need for the user to press any button or give any command. The electronic conversation occurs automatically and the devices form and network once the conversation has initiated. But there is a maximum range for which a connection will not be established. Bluetooth device has a transmitter and a receiver and the power of the device transmitter is the one that governs the range over which a Bluetooth device can open it. It was originally conceived as a wireless alternative to rs-232 data cables. We know rs-232 data cables are the serial data cables that are used for establishing serial communication between devices so Bluetooth was originally conceived as an alternative to that rs-232 data cables.
It specifies the entire suite of protocols going beyond the link layer to define the application protocols so this complete suite of protocols are called as profiles and this is for a range of applications suppose if you need an application we have a separate profile for every application let’s see two examples here:
So there is a profile for synchronizing a PDA with a personal computer PDA means personal digital assistant. So there is a separate profile for linking or synchronizing a personal digital assistant with a personal computer we will see another profile another profile gives a mobile computer access to a wired line. Suppose if we want to connect a mobile computer to a wired LAN we have a separate profile for achieving this and what about the network that is created by Bluetooth.
Now Bluetooth devices fall and they are one of three classes:
Class 1:
You have class one and they are the most powerful and can operate up to 100 meters. The maximum power of the Class 100 Mw and these types of Bluetooth are used in access point or USB adapters.
Class 2:
Class two they are the most common kind and operate up to 10 meter. The maximum power of this Bluetooth is 2.5 Mw and it is used in mobile devices, smart card readers and Bluetooth adapters.
Class 3:
Finally class three they are the least powerful and don’t go much beyond one meter and there maximum power is 1 Mw.
There are devices that can vary their transmit power so they can operate at different classes so their transmit power is adaptable.
Bluetooth working:
First let’s talk about network topologies in Bluetooth there are two types of network topologies:
- Piconet
- Scatternet
Piconet:
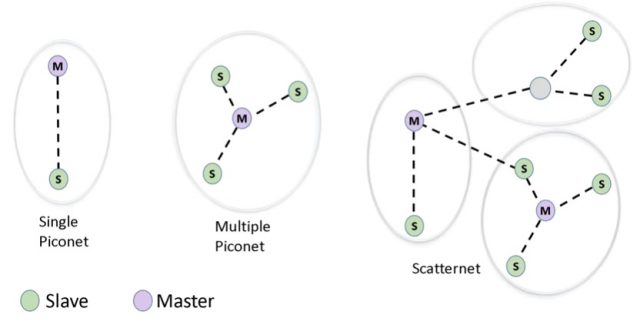
A single piconet is formed by one master and one slave. A multiple piconet is formed by one master and multiple slaves. Now a master is the device which initiates communication with other devices and indicates when a slave device may transmit also direct slave to slave communication is not possible. There can be a maximum of seven active slaves in the piconet which means only eight maximum devices including the master can communicate at any one time in a piconet.
The basic Bluetooth network configuration is called as a piconet. So this piconet is very important as far as a Bluetooth is concerned let’s see an example piconet where we have a master node which is connected with many nodes and these nodes are slave nodes. So in a piconet we will have only one master node some slave nodes so this is an example Bluetooth piconet. Let’s continue dealing with the Bluetooth now this is piconet it consists of a master device and up to seven slave devices. So when we say there can be only one master node in a piconet but to the maximum of seven slave nodes in a peak on any communication is the master and the slave so for example no two slave nodes can communicate with each other so any communication will be between a master and a slave and the slaves do not communicate directly with each other.
![]()
I have already explained this suppose if this PDA device wants to communicate with this mobile phone and this is also an active device and this is also an active device though these two are active these two slave devices cannot communicate with each other directly. So they have to communicate with each other through the master device only. So slaves do not communicate with each other and the slave can be parked that is it can be said to an inactive low-power state. Suppose if the slave is not at all communicating for a certain period of time in order to save the power that slave node can be parked that is it can be set to an inactive mode so that it enters into the low-power state. Normally these blue two devices are taking their power from the batteries. In order to sparingly use the batteries we are required to put the device in a low-power state. If the device is not active and that is why we have certain states in the Bluetooth configuration so far we have dealt with the basic piconet configuration.
Scatternet:
A scatter net is a combination of multiple piconet one thing to mention here about scatter net is that a master in one piconet can be a slave in another piconet. So you have here an example of this device Bluetooth device it’s in grey where it is a master for these two slaves but it is a slave for this master in the other piconet.
Like any other wireless technology Bluetooth technology use a spectrum or a frequency band that the device used to communicate.
Bluetooth spectrum:
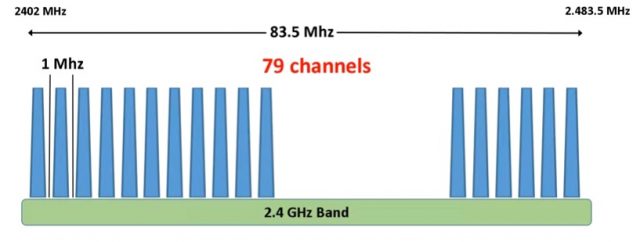
The Bluetooth devices exchange data in ISM band that is the industrial, scientific and medical band. The spectrum used by bluetooth start from 2402 mega Hertz and ends at 2483.5 mega Hertz and it consists of 79 channels having one megahertz bandwidth in each channel.
Frequency hopping:
Now why I am mentioning this well because Bluetooth devices use a technique called frequency hopping. In this technique the transmitter hops from one channel to another in pseudo random fashion determined by the masa and makes 1600 hops every second. let me clarify this a little bit more let’s consider the case of a smartphone transmitting a file to a computer with frequency hopping the data meaning the file will be transmitted in small pieces called packets. The first packet will be sent on a randomly selected channel let’s say channel 56 the next data packet will use a different channel also randomly selected let’s say channel 4 for instance and the process continue in this fashion till all packets are transmitted as I mentioned before there are 1600 frequency hops in every seconds which means every 625 microsecond a packet will be sent on a different frequency. So what is the benefit of this well the benefits of frequency hopping is to minimize eavesdropping. So it would be very difficult for a hacker to get into the network where frequencies are being changed every 625 microseconds and also it would minimize interference from other networks that use the ISM band. It is not just Bluetooth that use the ISM band but also a Wi-Fi used ISM band and the cordless phone use ISM band.
Uses of Bluetooth:
Let’s see a situation suppose you have some data in your mobile phone and your friend needs that data how you will save that data of course you have so many ways to send the data. You can send those data as an attachment in the email or you can send the data through Whatsapp but if you say you are going to send the data over email or Whatsapp it obviously needs the internet in order to send your data to the destination that is your friend’s mobile phone rather if we have Bluetooth adapters on both the devices we can simply create a personal area network and we can start transferring a data from one device to another device. The important point is that we don’t need internet connectivity for doing this.
Bluetooth devices:
The Bluetooth devices or adapters we have basically mini adapters they differ in its size and its functionality. In this example I have shown few Bluetooth adapters Bluetooth can be fixed devices and mobile devices. Suppose if we have a desktop computer if we need Bluetooth connectivity for that desktop computer what we should do so we can just purchase a Bluetooth adapter like this just plug this into the USB port of the desktop computer. So that we can have Bluetooth connectivity to our desktop computer where our desktop is a fixed device so no matter whether it is a fixed device or a mobile device. Bluetooth can establish short-range communication between fixed and mobile devices.

Top Bluetooth based devices Available on Amazon:
*Please Note: These are affiliate links. I may make a commission if you buy the components through these links. I would appreciate your support in this way!
Pros and Cons of Bluetooth:
Now let’s see the pros and cons of Bluetooth and we know the pros are its low cost and it’s easy to use it can also penetrate through walls but remember it is a short-range communication but still it can penetrate through walls and it creates an ad-hoc connection immediately without any wires because Bluetooth is a wireless technology. It is used for voice and data transfers Bluetooth speakers and Bluetooth headsets have become so popular. In today’s world Bluetooth speakers and Bluetooth headset are examples for voice transfers these are the pros of Bluetooth.
Now let’s see the cons of Bluetooth the first corners it can be hard when hence less secure and the second disadvantages it has a slow data rate and the third one is it has a small coverage range it can range up to 10 meters there is a class of Bluetooth which can range up 200 meters but still it has a very small range when compared to other technologies do you know there is a compete and technology for Bluetooth it’s ZigBee technologies.
Bluesnarfing:
The bluesnarfing is an attack of the unauthorized access of information from a wireless device through a Bluetooth connection often between phones desktops laptops and PDAs. So using Bluetooth technology if somebody tried to hack your network and steal your personal information then this attack is called as the blue snuffing attack. What an attacker can do using blue snuffing attack? So this blue snatching attack allows to calendar contacts list emails and text messages and on some phones user can copy pictures and private videos also so ultimately blue snuffing is the theft of information from the target device using unauthorized Bluetooth connection.
Discover more from Electronic Clinic
Subscribe to get the latest posts sent to your email.



